- SOLUTIONS
- SERVICES
- ABOUT US
- RESOURCES
- CONTACT
Wholesale Carriers – What if they go beyond protecting only their customers against fraud?
Fraudsters in telecom have always been attracted towards conducting cross border (international) frauds. Reasons such as lack of any country’s jurisdiction, anonymity, cross country non-cooperation and to top it inter operator & inter carrier competition have always provided the much exploited environment to conduct frauds.
Let us start with some industry recognized fraud loss statistics posted by CFCA. The top 4 fraud loss categories reported by CFCA in 2011 were:
- $4.96 Billion (USD) – Compromised PBX/Voicemail Systems
- $4.32 Billion (USD) – Subscription/Identity Theft
- $3.84 Billion (USD) – International Revenue Share Fraud
- $2.88 Billion (USD) – By-Pass Fraud
Considering a well accepted fact in telecom that “Subscription/Identity Theft” fuels other fraud types such as IRSF, all fraud types in the list somewhat end up generating (mostly) international traffic. Domestic traffic involvement in these frauds is found to be minimal.
Whenever an international fraud is identified by an operator at the source of traffic generation, it is generally followed by blocking the traffic to that destination as a preventive action. As an additional step, which is quite rare, a legal action is also carried out against some local goons involved in generation of the traffic identified as fraudulent. But, as we all know, the actual masterminds and the owners of the destinations identified as fraudulent remain free to explore another way of generating traffic to these destinations through any other operator, located anywhere in this world.
To make situation worse, a retail operator, sometimes is not even able to identify the root cause of the suspect spike or pattern seen to some of the non-risky or non-hot numbers/destinations as the traffic might be generated by exploiting certain arbitrage, FAS or other rogue interconnect revenue generation scenarios occurring down in the call transmission. Result, the operators give it a pass all because they do not detect any direct impact to their revenues.
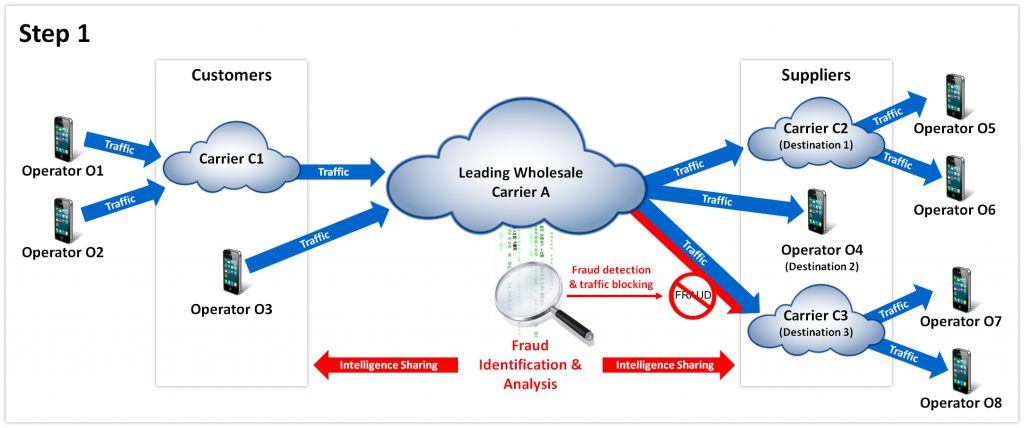
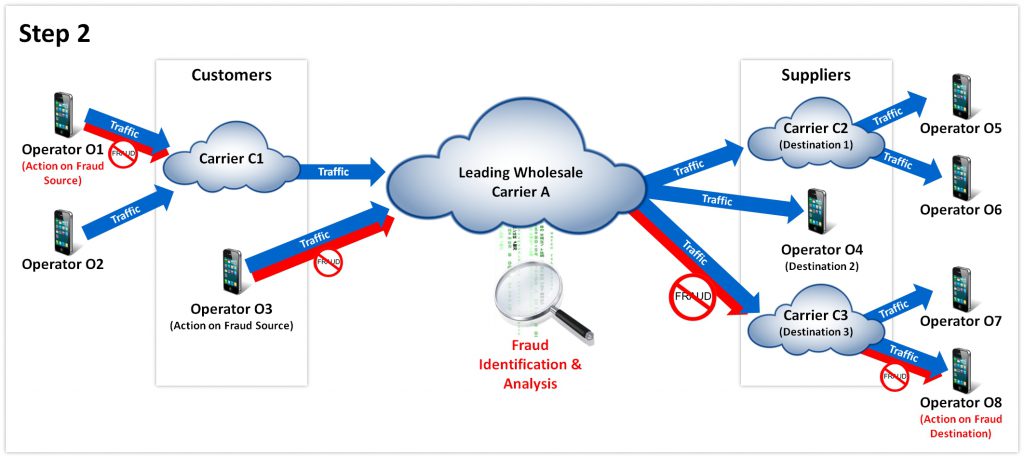
But, what if the wholesale carriers, who carry traffic to these destinations also join this unending fight against fraud, with a goal of not even notifying and protecting their direct customers to avoid contractual disputes, but with a higher goal of sharing their intelligence with all of their customers, suppliers and standard fraud forums, whenever a potential fraud case is identified.
Let us see how a wholesale carrier is better placed than a retail operator in identifying and protecting against the overall fraud chain which flourish on inflation of traffic to cross border (international) destinations:
- Wholesale operator sits in the middle of fraud source and fraudulent destinations which provide it a capability of having a holistic bird’s eye view over the fraudulent traffic from different customers (originations) to different suppliers (terminations) and can pin point the exact destination or number series which is receiving fraudulent traffic.
- Carrier can block the traffic to that destination or a specific number series within that destination, thereby not only protecting one customer to which the traffic belonged to, but all of them who may push a similar traffic anytime in future.
- Post blocking, the wholesale carriers are also capable of pressurizing the suppliers (other carriers or operators) to take action on the fraudulent parties or number series involved in the fraud racket by stopping the payments or the whole traffic to that supplier rather than individual series. Sharing information and risks against a rogue supplier in the wholesale market can also help avoid supplier to switch the partnership with other carrier.
- A wholesale carriers is also better placed than retail operators in identifying any specific suspect international traffic for fraud and fraud proofing the entire customer/supplier base through feedback. Intelligence collected through any fraud case identified over any customer traffic can be seamlessly passed on to all customers and suppliers in order to protect them from similar threat. This will specially empower the customers who are retail operators by helping them stop or reduce generation of fraudulent traffic at the source itself.
The following figures will help understand how the intelligence flow will help fight cross border telecom frauds:
Presence of a fraud identification and analysis mechanism in the wholesale carrier hands will also help the carrier meet the “anti fraud” clauses present in modern RFP requirements posted by the potential customers and will also help develops confidence to get into anti fraud amendments and best efforts based loss repayment contracts with the customers/suppliers, thereby earning more customers.
Said that, the approach will only be successful when there is enough participation from the wholesale carriers around the world, who because of the current telecom scenario, are also suffering from diminishing margins and dropping profits due to the cut throat competition.
This approach requires investment in order to empower the carriers with fraud analysis capability, which is not going to be made by medium and small players until and unless there is a huge value add shown to them or there is a direct pressure from majority of the customers and suppliers to act against frauds. And this can only happen when all the parties involved are determined for a fraud free environment and are able to create an environment of seamless intelligence sharing.