- SOLUTIONS
- SERVICES
- ABOUT US
- RESOURCES
- CONTACT
Telecom Fraud in 2026: Types, Emerging Risks & How AI-First Prevention Stops Revenue Leakage
Telecom fraud has evolved from isolated billing manipulation to a complex, AI-driven global threat ecosystem.
In 2026, Communication Service Providers (CSPs) are facing increasingly sophisticated fraud attacks across voice, SMS, roaming, digital payments, IoT, and 5G networks.
Fraud today is not just a revenue leakage problem it is a strategic business risk impacting EBITDA, customer trust, regulatory compliance, and brand reputation.
This pillar guide explores:
• The major types of telecom fraud impacting operators
• Why traditional fraud systems are failing
• Emerging AI-powered fraud risks
• Best practices for proactive prevention
• How Subex’s AI-First Fraud Management platform enables predictive fraud defense
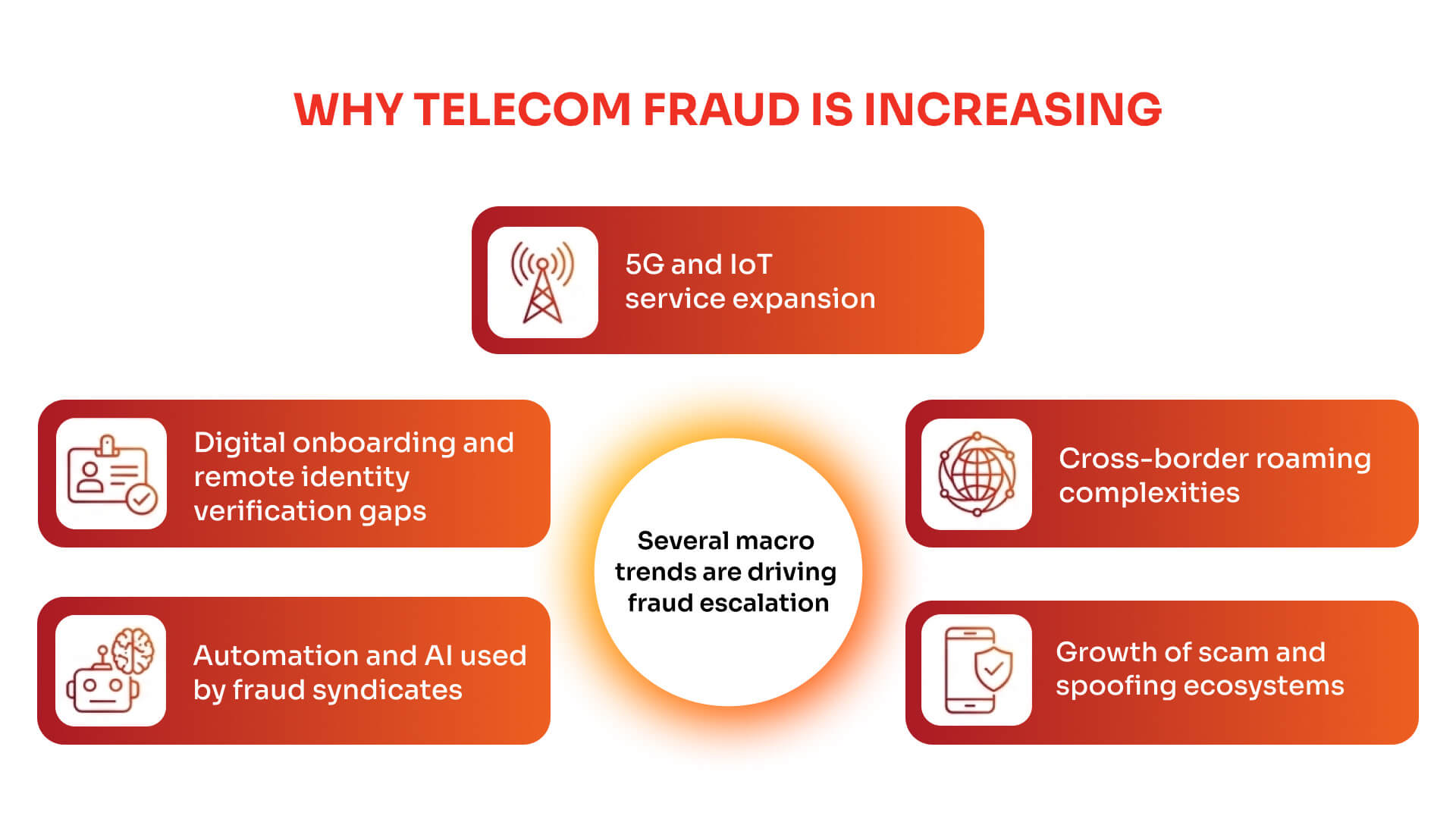
WHY TELECOM FRAUD IS INCREASING
Several macro trends are driving fraud escalation:
1. 5G and IoT service expansion
2. Digital onboarding and remote identity verification gaps
3. Cross-border roaming complexities
4. Automation and AI used by fraud syndicates
5. Growth of scam and spoofing ecosystems
Static rule‑based fraud detection systems cannot keep pace with fraud that evolves daily. Operators increasingly require machine‑learning‑driven detection models capable of identifying complex patterns in network and subscriber data.
MAJOR TYPES OF TELECOM FRAUD
1. International Revenue Share Fraud (IRSF)
What it is:
Fraudsters artificially generate high volumes of calls to premium-rate international numbers they control, earning a share of termination revenue.
Impact:
- Massive short-term revenue loss
- Interconnect disputes
- Regulatory complications
How Subex prevents it:
Subex uses machine‑learning classification models trained on historical IRSF call datasets. These models identify fraud indicators such as abnormal international call bursts, unusual destination patterns, and unexpected call duration distributions.
The model analyzes multiple data sources including call detail records (CDRs), SIP registration data, trunk/carrier information, and signaling events. Based on learned patterns from previously confirmed IRSF incidents, the system predicts whether a call session is likely fraudulent and assigns a confidence score to prioritize investigation.
2. SIM Box / Interconnect Bypass Fraud
What it is:
Fraudsters use SIM boxes or SIM farms to route international calls through local SIM cards, bypassing official interconnect routes and avoiding termination charges.
Impact:
- Direct revenue erosion
- Network congestion
- Reduced service quality
How Subex Detects It:
Detection relies on supervised machine learning classification models trained using labeled datasets of previously identified SIM box calls.
The model evaluates features such as abnormal call origination behavior, unusually high outgoing call volumes, repetitive call routing patterns, and mismatches between subscriber usage and typical traffic behavior.
The detection engine analyzes CDR data, subscriber information, recharge records, cell site information, and aggregated network traffic records to determine the probability that traffic originates from SIM box devices.
3. PBX Hacking & Traffic Pumping
What it is:
Fraudsters compromise enterprise PBX or VoIP systems to generate large volumes of international calls that are billed to the victim organization or telecom operator.
Impact:
- Enterprise disputes
- Operator revenue write‑offs
- Brand trust erosion
How Subex Detects It:
PBX hacking is detected using machine‑learning classification models trained on previously confirmed fraudulent traffic patterns.
The system monitors indicators such as abnormal international call spikes, irregular SIP registration activity, unusual trunk utilization, and traffic bursts outside normal business hours.
Using fixed‑line CDRs, SIP registration data, trunk/carrier information, and signaling events, the ML model evaluates whether call traffic likely originates from compromised PBX systems.
What it is:
Fraudsters place short missed calls from international premium numbers. Victims call back out of curiosity, resulting in expensive international charges.
Impact:
- Customer financial loss
- Increased churn
- Brand reputation damage
How Subex Detects It:
Subex applies supervised classification models trained on previously confirmed Wangiri call datasets.
The model identifies patterns such as extremely short call attempts, high volumes of missed calls from premium destinations, and abnormal callback behaviors.
Using historical labeled call data, the model predicts whether new call attempts resemble Wangiri attack patterns and assigns risk scores for proactive mitigation.
5. Subscription & Identity Fraud
What it is:
Fraudsters impersonate legitimate subscribers and request SIM replacements, allowing them to intercept calls and SMS messages including banking OTPs.
Impact:
- Financial fraud
- Account takeover
- Regulatory compliance risks
How Subex Detects It:
Detection uses subscriber behavioral profiling and anomaly detection models.
Machine learning monitors predefined behavioral metrics such as usage volumes, recharge patterns, billing history, and subscription activity. Significant deviations from established patterns trigger alerts for investigation.
These models analyze subscriber data including usage CDRs, billing records, recharge history, subscriber information, and transaction activity to detect identity‑based fraud risks.
WHY LEGACY FRAUD SYSTEMS FAIL
Traditional fraud management systems rely heavily on static rules, threshold alerts, and manual investigations.
This results in:
- High false positives
- Slow detection times
- Fraud losses before detection occurs
- Investigator fatigue
Modern fraud prevention requires advanced analytics, machine learning models, and automated mitigation capabilities.
Fraud management must shift from reactive detection to predictive prevention.
THE SUBEX AI-FIRST FRAUD MANAGEMENT APPROACH
Subex delivers a unified, AI-powered fraud management ecosystem designed specifically for telecom operators.
Core Capabilities:
1. Real-Time Fraud Detection
Continuous monitoring across voice, SMS, roaming, digital services, and emerging 5G use cases.
2. Hybrid Detection Engine
Combination of rule-based logic and advanced machine learning models.
3. Behavioral Analytics
Detection based on deviations from normal usage patterns.
4. GenAI-Powered Investigation Agents
AI-assisted workflows that accelerate investigation and reduce manual workload.
5. Fraud Intelligence Repository
Global risk database of high-risk destinations, CLI spoof indicators, and suspicious identities.
6. Automated Mitigation
Integrated workflows enabling immediate blocking and response.
BEST PRACTICES FOR TELECOM FRAUD PREVENTION IN 2026
• Deploy real-time analytics across all services
• Use behavioral and ML-based anomaly detection
• Integrate fraud and revenue assurance insights
• Leverage global fraud intelligence feeds
• Automate response workflows
• Continuously retrain detection models
Frequently Asked Questions About Telecom Fraud
1. What is telecom fraud?
Telecom fraud refers to unauthorized activities that exploit telecom networks to generate illegal revenue or avoid legitimate charges. Fraudsters manipulate voice, SMS, roaming, or digital services to create financial losses for operators and customers. Common examples include IRSF, SIM box fraud, Wangiri scams, and SIM swap fraud.
2. What is a telecom fraud management system (FMS)?
A telecom fraud management system (FMS) is a software platform used by telecom operators to detect, prevent, and investigate fraudulent activities across their networks. It analyzes telecom data such as call detail records (CDRs), signaling events, and subscriber behavior to identify suspicious patterns and stop fraud before significant revenue loss occurs.
3. What are the most common types of telecom fraud?
The most common telecom fraud types include International Revenue Share Fraud (IRSF), SIM box fraud, Wangiri scams, PBX hacking, SIM swap fraud, robocalling, and SMS spoofing. These fraud schemes exploit telecom networks to generate illegal revenue or steal customer data, costing the telecom industry billions each year.
4. What is IRSF fraud in telecom?
International Revenue Share Fraud (IRSF) occurs when fraudsters generate large volumes of calls to premium-rate international numbers they control. Telecom operators unknowingly pay high termination charges, while fraudsters receive a share of the revenue, resulting in significant financial losses.
5. What is SIM box fraud?
SIM box fraud occurs when fraudsters use devices called SIM boxes to route international calls through local SIM cards. This bypasses official telecom interconnect routes and avoids termination charges, causing revenue loss for telecom operators and degrading network performance.
6. How does AI help detect telecom fraud?
AI helps detect telecom fraud by analyzing large volumes of telecom data such as call detail records, subscriber behavior, and signaling events. Machine learning models identify abnormal patterns, detect suspicious activities, and predict fraud risks, enabling operators to prevent fraud before major financial damage occurs.
7. Why are traditional fraud detection systems ineffective?
Traditional fraud detection systems rely on static rules and threshold-based alerts. These systems struggle to detect modern fraud patterns that evolve rapidly and often generate large volumes of false alerts. Machine learning models provide more accurate detection by analyzing behavioral patterns and historical fraud data.
8. How can telecom operators prevent fraud?
Telecom operators can prevent fraud by deploying real-time fraud detection systems, machine learning models, and behavioral analytics. Integrating fraud intelligence databases, monitoring network traffic continuously, and automating mitigation workflows help operators detect threats early and reduce revenue leakage.
FAQ SCHEMA (JSON-LD)
Below is the structured data to implement on the blog page:
CONCLUSION
Telecom fraud in 2026 demands intelligence-led, AI-powered defense mechanisms.
Operators that transition from reactive detection to predictive prevention will protect revenue, strengthen customer trust, and ensure sustainable growth.
Subex’s AI-First Fraud Management platform empowers CSPs to detect, prevent, and mitigate fraud in real time transforming fraud management into a strategic growth enabler.
Discover how Subex’s AI-First Fraud Management platform enables real-time detection, automated mitigation, and predictive fraud prevention.